媳妇上周入手这款手机,主要研究Android 的UI,她们公司要做客户端。感觉很行,最不爽的,是一大堆定制软件,看着都烦,有些软件可以在软件管理卸载掉,有些需要root,/cust/chinatelecom/cn/app 目录下的OEM app,大都可以删掉。照着这个帖子 《华为C8812E刷机解锁ROOT教程(附带ROM下载地址)》,基本可以搞定。
很郁闷的是,
$ adb devices
List of devices attached
???????????? device有一串问号,以为是驱动连不上,试了 adb shell 居然可以进入,原来它就是这样!还有更变态的:
$ adb logcat
info: log device is empty!关闭了log,解决方法:
http://stackoverflow.com/questions/6941710/unable-to-open-log-device-dev-log-main-no-such-file-or-directory
Dial this: *#*#2846579#*#*
Service menu will appear.
Go to “ProjectMenu” -> “Background Setting” -> “Log Setting”Open “Log switch” and set it to ON.
Open “Log level setting” and set the log level you wish.Reboot the phone.
有了root,那么限制你的,只有你的想象力了。删除的apk路径在:
/system/app
/system/delapp
/data/cust/app
/data/cust/delapp
/cust/chinatelecom/cn/app
/cust/chinatelecom/cn/delapp上面的路径含有 delapp 的,是在管理软件里手动卸载后,在相应的 delapp 目录保存一份。删除之前,要清楚知道你在干什么,如果误删了,只得重新刷机。
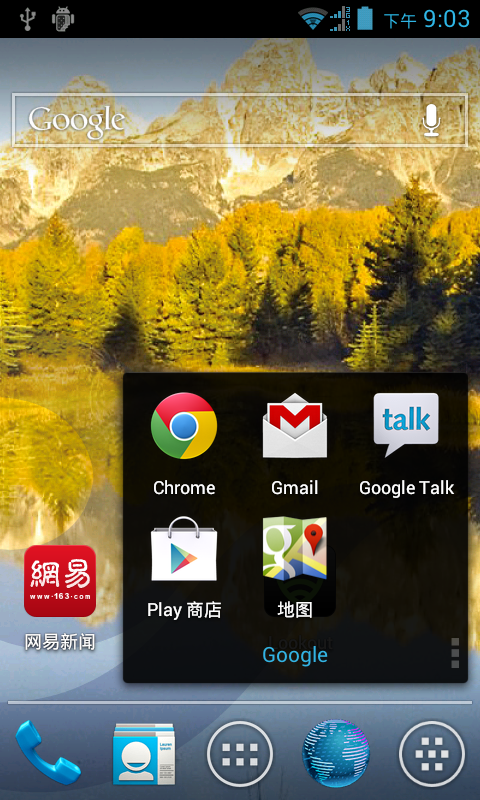
想装上谷歌应用包 gapps,到 http://wiki.cyanogenmod.org/wiki/Latest_Version/Google_Apps 找最新的20121128 gapps 包,90多M,手机的 /system 分区没那么多空间,删掉没用的应用,还是不够,最后选用 gapps-ics-20120422-signed,50M.
$ adb remout
$ cd ~/Downloads/gapps-ics-20120422-signed
$ adb push system/ /system如果误删了某个软件,怎么办?可以到华为官方下载ROM, 使用 split_updata.pl 打开 UPDATE.APP,提取 system.img。
$ perl split_updata.pl UPDATE.APP
Extracted output/file01.mbn
Extracted output/file02.mbn
Extracted output/boot_versions.txt
Extracted output/file04.mbn
Extracted output/file05.mbn
Extracted output/upgradable_versions.txt
Extracted output/file07.mbn
Extracted output/file08.mbn
Extracted output/file09.mbn
Extracted output/version.txt
Extracted output/file11.mbn
Extracted output/appsboothd.mbn
Extracted output/appsboot.mbn
Extracted output/file14.mbn
Extracted output/boot.img
Extracted output/file16.mbn
Extracted output/system.img
Extracted output/file18.mbn
Extracted output/userdata.img
Extracted output/file20.mbn
Extracted output/file21.mbn
Extracted output/recovery.img
Extracted output/file23.mbn
Extracted output/splash.raw565
Extracted output/file25.mbn
deli@deli-ThinkPad-T42:~/a/output$ du -sh *.img
382M boot.img
4.0K recovery.img
189M system.img
3.7M userdata.img
但发现 C8812的官方包解包后的boot.img实际上是system.img,system.img实际上是userdata.img,有点变态。boot.img 是 ext4格式,这个好办:
$ file boot.img
boot.img: Linux rev 1.0 ext4 filesystem data, UUID=57f8f4bc-abf4-655f-bf67-946fc0f9f25b (needs journal recovery) (extents) (large files)
$ mkdir e
$ sudo mount -t ext4 -o loop boot.img e
$ cd e/
$ ls
app build.prop delapp fonts lib ts.conf usr wifi
bin cdrom etc framework media tts vendor xbin
取你所取。
Leave a Reply